Chinese State-Sponsored Technology Theft: A Global Threat
The coordinated warnings from the FBI and MI5 regarding Chinese state-sponsored technology theft represent a significant escalation in the ongoing struggle for global technological dominance․ These agencies are not merely issuing cautions; they’re painting a stark picture of a sophisticated, well-funded, and persistent campaign aimed at acquiring sensitive intellectual property from businesses and governments worldwide․ The implications are far-reaching, affecting national security, economic competitiveness, and the future of innovation․ This is not a localized issue; it’s a global threat requiring a comprehensive response․
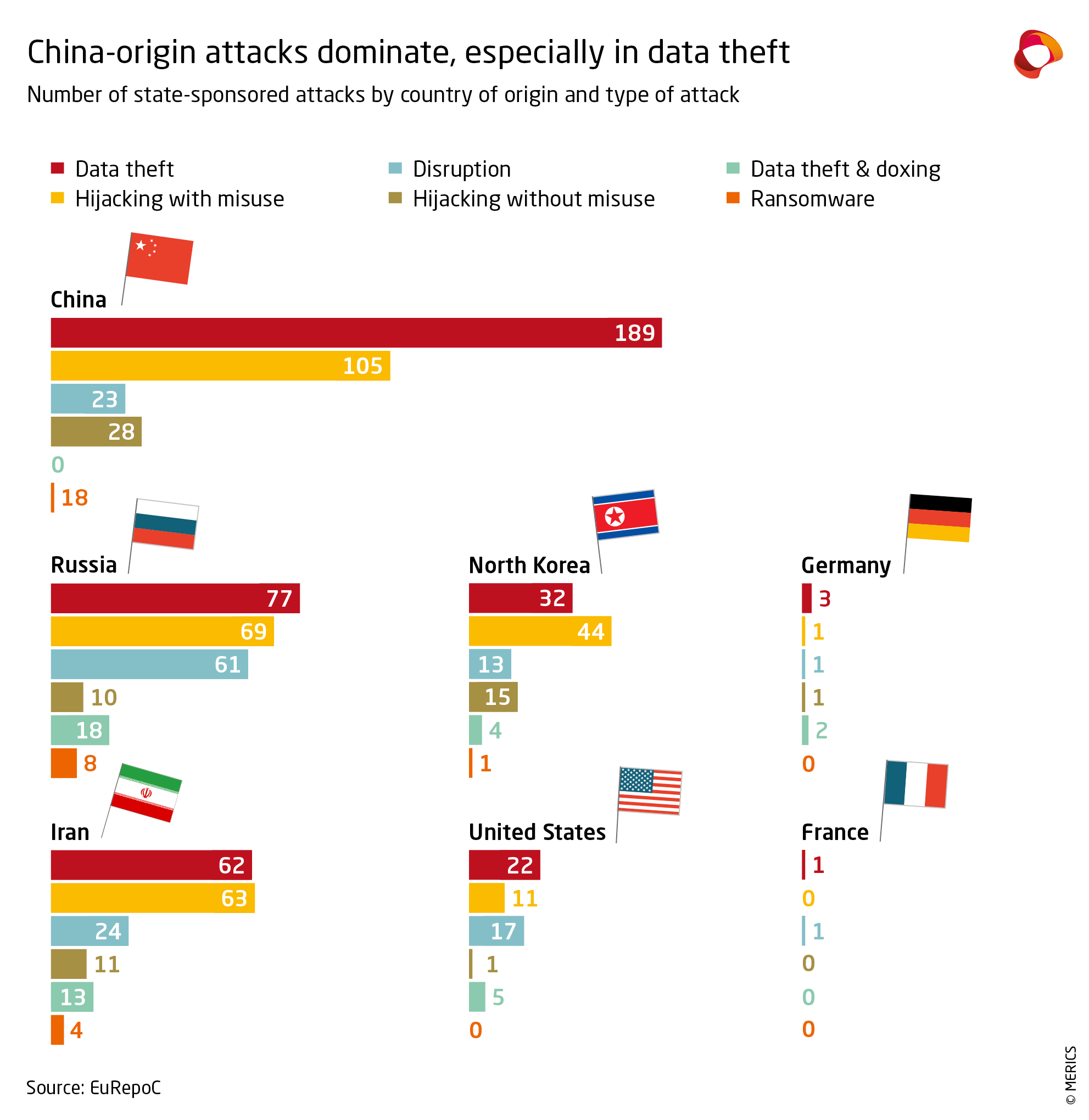
Understanding the Scale of the Threat
The scale of the Chinese government’s alleged technology theft operation is staggering․ Reports suggest a vast network of operatives, including state-sponsored hackers, researchers posing as legitimate business partners, and even insiders compromised through bribery or coercion․ The targets are diverse, ranging from cutting-edge semiconductor technology to sensitive military research and even seemingly innocuous data that, when pieced together, can reveal valuable trade secrets․ The methods employed are equally varied and often involve a combination of cyberattacks, physical espionage, and social engineering․
Cyber Espionage: The Digital Battlefield
Cyber espionage forms a crucial element of the Chinese government’s strategy․ Sophisticated hacking groups, often linked to the Chinese military or intelligence services, are known to target companies and research institutions across various sectors․ These attacks often involve the exploitation of zero-day vulnerabilities – software flaws unknown to developers – allowing hackers to gain unauthorized access to sensitive systems․ Data breaches can expose everything from product designs and source code to customer databases and financial information․ The consequences can be devastating, resulting in significant financial losses, reputational damage, and even national security risks․
Human Intelligence: The Human Factor
Beyond the digital realm, the Chinese government also leverages human intelligence (HUMINT) to acquire sensitive technology․ This often involves cultivating relationships with individuals within target organizations, potentially through bribery, blackmail, or the promise of lucrative employment opportunities․ These insiders can provide valuable intelligence, allowing access to sensitive information or facilitating the theft of physical materials․ The effectiveness of HUMINT underscores the importance of robust internal security measures and thorough background checks for employees handling sensitive information․
The Economic Impact: A Global Race
The economic consequences of this intellectual property theft are far-reaching․ The loss of competitive advantages, the cost of remediation, and the disruption of business operations all contribute to significant financial burdens․ Innovation is hampered as companies struggle to protect their research and development efforts․ This not only affects individual businesses but also undermines national competitiveness, especially in technologically advanced sectors where intellectual property forms the foundation of economic growth․ The race for technological supremacy is becoming increasingly fraught with challenges, and the theft of intellectual property is a significant obstacle․
Protecting Your Intellectual Property: A Multi-Layered Approach
Protecting intellectual property from state-sponsored theft requires a multifaceted strategy․ It is not sufficient to rely on a single security measure; instead, a layered approach combining multiple techniques is essential․
- Robust Cybersecurity: Implementing strong cybersecurity measures is paramount․ This includes regularly updating software, employing strong passwords and multi-factor authentication, regularly backing up data, and conducting penetration testing to identify vulnerabilities․
- Employee Training: Educating employees about the risks of social engineering and phishing attacks is crucial․ Regular security awareness training can significantly reduce the likelihood of successful attacks․
- Physical Security: Secure physical access to facilities where sensitive information is stored is essential․ This includes access control systems, surveillance cameras, and secure storage solutions․
- Data Encryption: Encrypting sensitive data both in transit and at rest provides an added layer of protection, making it much more difficult for unauthorized individuals to access the information․
- Legal Counsel: Consulting with legal professionals specializing in intellectual property law can provide valuable guidance on protecting your assets and pursuing legal action if necessary․
Collaboration and Information Sharing
Collaboration between governments, businesses, and research institutions is crucial in combating this global threat․ Sharing information about observed threats, best practices, and successful mitigation strategies can significantly improve collective defenses․ Open communication channels enable a more coordinated response, reducing the effectiveness of state-sponsored theft attempts․
The Role of International Cooperation
Addressing the issue of state-sponsored technology theft requires strong international cooperation․ While individual nations can implement robust domestic security measures, a coordinated global effort is needed to effectively deter and counter these activities․ International agreements, sanctions, and collaborative intelligence sharing are crucial components of a comprehensive strategy․ This requires a concerted effort from nations to establish clear norms of behavior in cyberspace and to hold accountable those who engage in malicious cyber activities․
The Need for Transparency and Accountability
Transparency and accountability are essential in fostering a secure international environment․ Governments need to be open about the threats they face and the measures they are taking to address them․ This transparency not only helps to build trust but also facilitates collaborative efforts to counter state-sponsored theft․ Similarly, holding perpetrators accountable for their actions, through sanctions or other legal mechanisms, is crucial in deterring future attempts․
The Long-Term Implications
The long-term implications of unchecked state-sponsored technology theft are profound․ It threatens not only economic competitiveness but also national security and the integrity of scientific research․ The erosion of trust in open collaboration and the chilling effect on innovation are significant concerns․ Without effective countermeasures, the global technological landscape will become increasingly distorted, favouring those who engage in illicit activities․
- Diminished Innovation: The fear of intellectual property theft can stifle innovation as companies become more hesitant to invest in research and development․
- National Security Risks: The theft of sensitive military or critical infrastructure technologies poses significant national security risks․
- Economic Inequality: Unethical acquisition of technology can lead to significant economic imbalances between nations․
- Erosion of Trust: The pervasive nature of state-sponsored theft can erode trust between nations and hinder international collaboration․
The warnings from the FBI and MI5 are not simply cautionary tales; they represent a stark reality․ The Chinese government’s alleged campaign to steal technology poses a serious threat to global security and economic stability․ A multi-layered, collaborative approach, incorporating robust cybersecurity measures, strong international cooperation, and a commitment to transparency and accountability, is vital to mitigating this pervasive threat․ Only through concerted efforts can we safeguard our intellectual property and ensure a fair and innovative global technological landscape․ The future of innovation hinges on our collective ability to address this challenge effectively․ The implications of inaction are far too significant to ignore․ We must act decisively and collaboratively to counter this threat․ The consequences of complacency are simply unacceptable․
